My mastodon feed is full of IT security specialist talking about the xz affair where someone let a backdoor in some library.
But beside showing the two side of Free/Libre software (anybody can add a backdoor, and anybody can spot it), I have no idea how it impacts the average person. Is it a common library or something used only by specific application ? Would my home-grade router protects me ?
How does the xz incident impacts the average user ?
It doesn’t.
Average person:
- not running Debian sid, Fedora nightly,
Arch, OpenSUSE Tumbleweed, or tbh any flavour of Linux. (Arch reportedly unafffected) - ssh service not exposed publicly
The malicious code was discovered within
a day or twoa month of upload iirc and presumably very few people were affected by this. There’s more to it but it’s technical and not directly relevant to your question.For the average person it has no practical impact. For those involved with or interested in software supply chain security, it’s a big deal.
Edit:
Corrections:- OpenSUSE Tumbleweed was affected; Arch received malicious package but due to how it is implemented did not result in compromised SSH service.
- Affected package was out in the wild for about a month, suggesting many more affected systems before malicious package was discovered and rolled back.
I don’t even understand what anyone in this thread is saying.
That’s not an invitation, please don’t explain Linux to me.
I’m just saying this means nothing for average people.
It could have meant a lot to the average person if it wasn’t caught. If this was some adversary, they could have used it to cripple critical infrastructure in the largest cyber attack in history.
Luckily it was caught before this software was rolled out to really anything that should be in prod.
It actually means a lot for average people. Only because you are not able to comprehend some things, does not mean you are not affected by it. But feel free to keep on using Windows XP.
You forgot about OpenSUSE Tumbleweed, it also shipped the infected package. I had to update to a newer non-infected version of xz.
Thanks, SUSE completely slipped my mind
Not just a day, a full month the backdoor was available. On the Arch Repo, v5.6.0 was uploaded on February 24th. Will be similar to other repos.
I believe 5.6.0 was in Debian testing for almost a month too.
Thanks for the correction. A full month is much more problematic.
What about vpn behind WireGuard/OpenVPV?
I would presume no?
- not running Debian sid, Fedora nightly,
Quick summary:
- only impacts Debian and Linux distributions that utilize RPM for packages
- only impacts cases where liblzma is compiled from a tarball, rather than cloned source repository or precompiled binary
- only impacts x64 architecture
- introduced in liblzma 5.6.0 which was released in late February so only impacts installs receiving updates to liblzma since then
liblzma is a library for the lzma compression format. Loosely, this means it’s used by various other pieces of software that need this type of compression, rather than being an application itself.
It is very widely used. It comes installed on most major Linux distributions and is used by software like openssh, one of the standard remote connection packages.
However, since it was only in the tarball, you wouldn’t see it widely until debian, fedora, et al release a new version that includes the latest liblzma updates. This version hadn’t been added to any of the stable release channels yet, so the typical user wouldn’t have gotten it yet.
I believe this would have gone out in debian 12.6 next week, and the attacker was actively petitioning fedora maintainers to get it added to fedora 40 & 41
The interesting thing about this situation was how much effort the attacker put in to gain trust just to get to the point where they could do this, and how targeted the vulnerability seems to have been. They tried very hard to reduce the likelihood of being caught by only hitting a limited set of configurations
For exploits like this, most of the risk is in services you use. Websites, power company customer database, etc. are at risk of customer data dumps leaking.
Be extra alert for targeted scams and phishing, i.e. Phil from HBO Max customer department calling and asking to correct your payment details and he sounds very convincing because he knows your username, viewing history, etc.
And be extra fast with installing any security updates on all your stuff.
I’m one of those security specialists (although not on mastodon). To be clear, if a vulnerable version of libxz were included in a distribution that we actually use; this would be an all hands on deck, drop everything until it is fixed emergency.
Having said that, for an average user, it probably doesn’t matter. First, many users just don’t have the vulnerable version installed. All things considered, it was found very quickly; so only rolling release distros would have it. Additionally, it appears that only .deb or .rpm based distributions would have it. Not because they are particularly vulnerable, the attack explicitly tests for it.
However, lets set all of this asside and assume a typical use is running a vulnerable system. In my assessment, the risk to them is still quite low. With most vulnerabilities, the hard part is discovering it. Once that happens, the barrier to exploiting it is relatively low, so you get a bunch of unrelated hackers trying to exploit any system they can find. This case is different; exploiting it requires the attackers private key. Even though the attack is now widely known, there is still only 1 organization capable of using it.
Further, this attack was sophisticated. I’m not going to go as far as others in saying that only a state actor could do it. However, it is hard to think of anyone other than a state actor who would do it. Maybe a group of college kids doing it for the
lolzresearch? But, if the motivation us lolz, I don’t see them pivoting to do anything damaging with it. And even if they wanted to, there would still only be a handful of them. In short, this is one of those cases where obscurity works. Whoever did this attack does not know or care about Joe the Linux user; and they were probably never going to risk burning it by exploiting it on a large scale.However, setting all of that asside, suppose you were using vulnerable software, and someone with the private key is interested in your home system. First, you would need to be running OpenSSH on a remotely accessible interface. [0]. Second, you would need your firewall to allow remote SSH traffic. Third, you would need your router to have port forwarding enabled; and explicitly configured to forward traffic to your OpenSSH server [1].
If all of that happens; then yes, you would be at risk.
[0] Even though the attack itself is in the libxz library, it appears to specifically target OpenSSH.
[1] Or, the attacker would need some other mechanism to get on the same network as you.
The average user? Likely doesn’t. the package is for Linux, so that removes any windows users.
The version was only on “bleeding edge” releases, so if you are on a lts release you will likely be ok.
Ubuntu 16 is lts, right?
16.04 is LTS. 16.10 hasn’t been updated or supported for 6 years
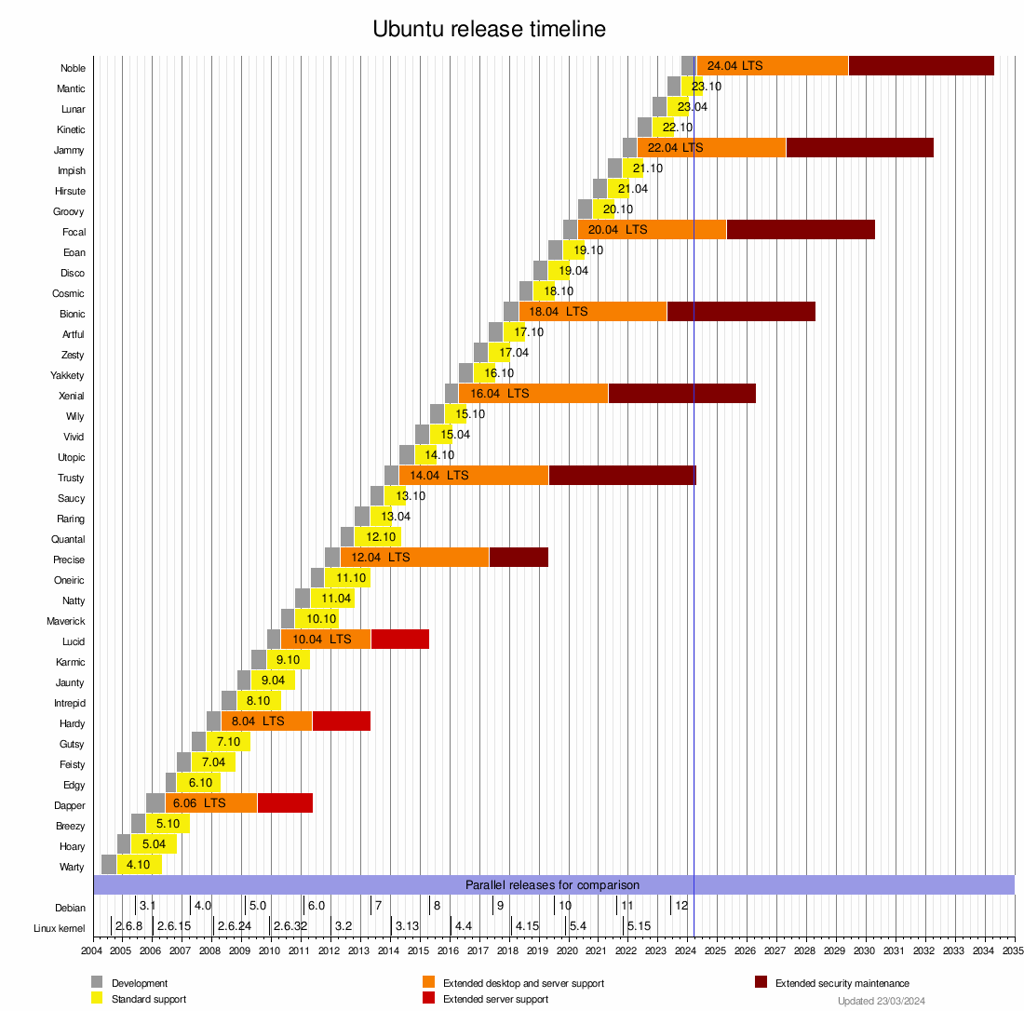
So it’s safe! No new malware in there!
only someone running arch or debian sid or an bleeding edge rolling release on an internet exposed ssh port. the idea of that configuration would sound ludicrous. even so we should be building off git repos not tar balls.
the weird part this situation has made me feel safer. the amount of work that went into social engineering this and it only lasted a month tops for people that run distros that would just not be or should not be used as an exposed server ever.
it shows open source works. This is more embarrassing than anything and we deserve it. We need to pay core library devs and have a mechanism that core libraries can be handed off to a trusted org.while another upstream maintainer can be found or the project shut down and other projects move away from the un maintained project. When the person maintaining the project gets burned out or has other issues.
From the archlinux.org news post on the issue.
Arch does not directly link openssh to liblzma, and thus this attack vector is not possible.
why does everyone keep mentioning arch?
Because Arch was one of the distros that distributed the backdoored xz package, though they claim no vulnerability to due to their implementation.
so… they didn’t distribute the backdoored package did they?
Bruh ask Google the question instead of making a stranger figure it out for you. If you want an answer typed up for you go ask a LLM.
I already knew the answer. arch was not affected. hence why i asmed why it kept being mentioned.
I wasn’t asking if arch was affected. I was asking why you keep regurgitating this clearly wrong information (if you bothered to google it, of course)
So no, google could not have answered my question. And if you do use llms for answers, I feel sorry for you
I’m not sure I agree with that, Arch 100% should continue to be mentioned. Just because the Trojan didn’t launch due to the fact that Arch’s environment didn’t meet its criteria, doesn’t mean you should keep a known malicious package on your system.
People keep preaching to the heavens that Arch was not affected by it, but they don’t always state that Arch was infected by it, it just never binds the library to SSHD like Debian systems do (for systemd notifications) so the attack vector is never made.
The arch Wiki official statement on it is that you should remove the malicious package and do a full system update. Which should be common sense, but people have to be aware that the system is infected by it in order to know that they have to remove it. A process that if Arch was never mentioned as being involved users wouldn’t think to do
I don’t even have xz installed on my machine. Could anyone clue me in for what it is normally used?
It’s a library/tool for a specific type of compression. You may have seen .tar.xz files.



